Internal Address Review Covering 10.11.12.18 and Reports
The discussion centers on the internal address block 10.11.12.18 and the associated reports. It emphasizes defined scope, data-driven indicators, and governance boundaries. The approach is methodical, with attention to access controls and verifiable ownership. Findings must translate into actionable steps that prove repeatable processes. The implications for visibility and risk management are clear, yet practical gaps remain, inviting closer scrutiny of who can see what and why.
What the 10.11.12.18 Block Represents and Why It Matters
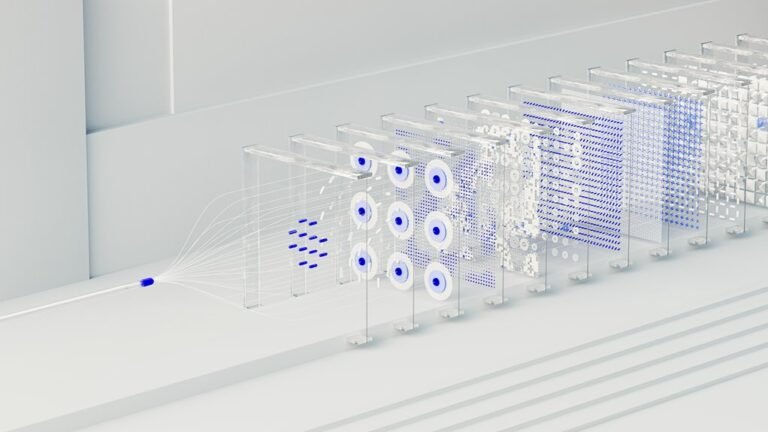
The 10.11.12.18 block represents a specific, routable address space within a larger network, designated for targeted examination and reporting. It clarifies an Internal Address role in practice, signaling intentional scope boundaries.
In this context, Network Segmentation emerges as a structural principle, directing access controls and containment.
Observations remain skeptical, precise, and purposeful, aligning with a freedom-seeking, analytical posture.
Reading the Internal Address Report: Data Points That Matter
Reading the internal address report requires focusing on key data points that reveal usage patterns, scope, and risk indicators without conflating correlation with causation.
The analysis emphasizes data quality, isolating anomalies, and traceability, with disciplined review of logs and timelines.
This stance strengthens incident response readiness, prioritizing verifiable signals over assumptions and enabling skeptical, objective decision making.
Access Controls and Ownership: Who Can See What and Why It’s Important
Access controls and ownership define who can view data, and under what circumstances, across the internal address framework.
The analysis remains precise: access controls must be verifiable, ownership visibility audited, and governance accountability maintained.
Clear delineation prevents overreach, supports compliance reporting, and preserves user autonomy.
Skepticism guards against hidden permissions while preserving transparent access in pursuit of freedom and responsible stewardship.
Turning Findings Into Action: Practical Steps for Visibility, Governance, and Compliance
Turning findings into action requires a disciplined translation of observed gaps into concrete governance steps, with each measure tied to measurable visibility and compliance outcomes.
The approach criminates ambiguity, assigns governance roles, and documents responsibilities to close visibility gaps.
It emphasizes repeatable processes, objective metrics, and skeptical validation to ensure that action translates into durable controls and auditable accountability.
Conclusion
The analysis concludes that the 10.11.12.18 block requires disciplined governance, verifiable ownership, and auditable processes to prevent ambiguity in scope and risk. Data points must be cross-validated against policy, with access controls explicitly documented and periodically tested. Findings should drive concrete, measurable steps rather than observations alone. In this framework, governance is kept honest by repeatable procedures—like a compass in a fog—ensuring visibility, accountability, and sustained compliance.