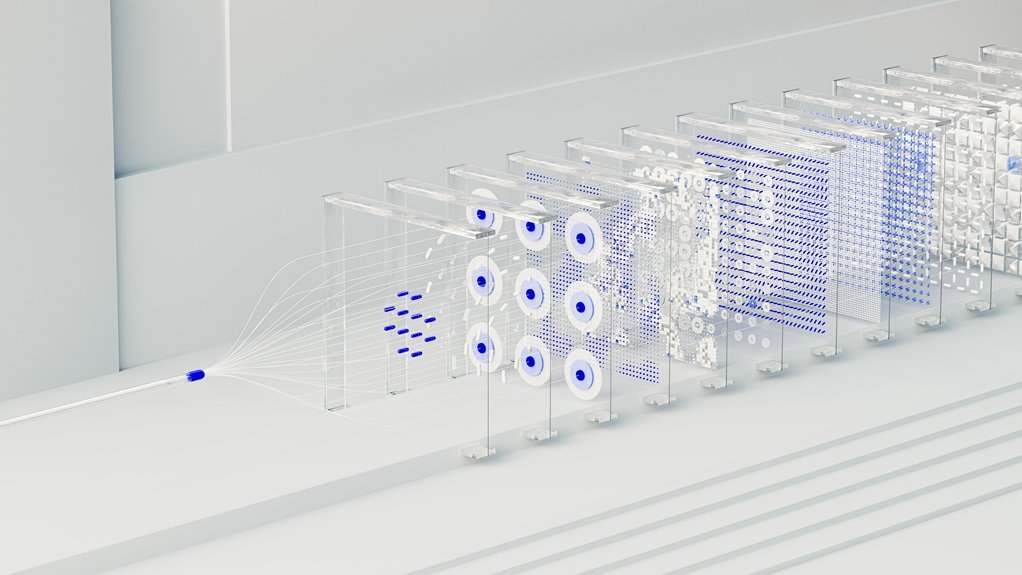
Neural Flow 2015475477 Cyber Node
The Neural Flow 2015475477 Cyber Node integrates real-time computation within a distributed cyber-physical framework. It emphasizes adaptive load distribution, latency-aware scheduling, and deterministic throughput across heterogeneous edge resources. Privacy, security, and interpretability are embedded in governance and auditing processes. The architecture enables resilient autonomy, edge collaboration, and continuous threat monitoring. Yet crucial trade-offs remain between latency, throughput, and reliability, inviting deeper examination of orchestration strategies and real-world deployments.
What Is Neural Flow 2015475477 Cyber Node and Why It Matters
Neural Flow 2015475477 Cyber Node represents an integrated computational architecture designed to facilitate real-time data processing, decision-making, and autonomous control within a distributed cyber-physical framework. The model emphasizes neural flow principles, enabling resilient cyber node operations.
Edge orchestration coordinates sensor-to-edge tasks, while workload distribution balances compute load, reducing latency and enhancing reliability for adaptive, autonomous systems.
How the Cyber Node Orchestrates Neural Workloads Across Distributed Edges
The Cyber Node coordinates neural workloads across distributed edges by implementing a layered orchestration framework that maps sensory streams to edge compute resources, optimizes task placement, and enforces latency-aware scheduling.
It analyzes resource diversity, enforces deterministic throughput, and coordinates inter-node communication.
Edge orchestration enables adaptive workload distribution, reducing bottlenecks, while maintaining transparency, resilience, and scalable performance across heterogeneous, decentralized infrastructures.
Privacy, Security, and Interpretability in Real-Time Networks
How can Real-Time Networks ensure robust privacy, security, and interpretability without compromising performance? The analysis surveys privacy concerns, security risks, and interpretability challenges within data governance and real time monitoring. It evaluates edge orchestration and workload delegation, advocating privacy preserving mechanisms, auditable processes, and model robustness. Transparent auditability enables freedom through disciplined governance, while continuous monitoring mitigates evolving threats and sustains trust.
Use Cases and Trade-Offs: Latency, Throughput, and Real-World Impact
Analysts assess use cases and the accompanying trade-offs by mapping application requirements to measurable performance metrics, focusing on latency, throughput, and real-world impact. The analysis emphasizes privacy metrics, latency benchmarks, and security considerations, guiding throughput optimization while balancing explainability methods and edge compliance.
Outcomes hinge on precise evaluation, trade-off transparency, and disciplined, methodical assessment of operational feasibility and freedom-enabled advancement.
Conclusion
The Neural Flow 2015475477 Cyber Node embodies a rigorous, analytically grounded approach to edge-centric neural orchestration, balancing latency, throughput, and security in real time. Its layered governance and adaptive load distribution enable deterministic performance while preserving privacy and interpretability. A hypothetical regional smart-grid deployment illustrates this: sensors and controllers across substations harmonize workloads to prevent outages, with tamper-evident auditing and threat monitoring ensuring resilient, auditable operations despite heterogeneous hardware and fluctuating networks.