Call Monitoring Documentation About 8007025d and Activity Logs
8007025d denotes a disruption in call monitoring sessions, indicating failure to establish or sustain oversight under defined conditions. Activity logs must be collected with source data, timestamps, and metadata, then standardized and stored immutably with provenance tagging and strict access controls. The documentation should reflect auditability and reproducibility, enabling governance and incident reconstruction. This framework invites scrutiny of collection methods, structure, and compliance, ensuring the discipline extends to future incidents and ongoing oversight gaps.
What 8007025d Means for Call Monitoring and Logs
The code 8007025d denotes a specific status related to call monitoring systems, indicating that a monitoring session could not be established or maintained under defined conditions.
In this context, the entry aligns with monitoring terminology, signaling a gap in ongoing oversight. Analysts assess implications for log integrity, ensuring records remain verifiable while documenting the anomaly for future audits and freedom-minded governance.
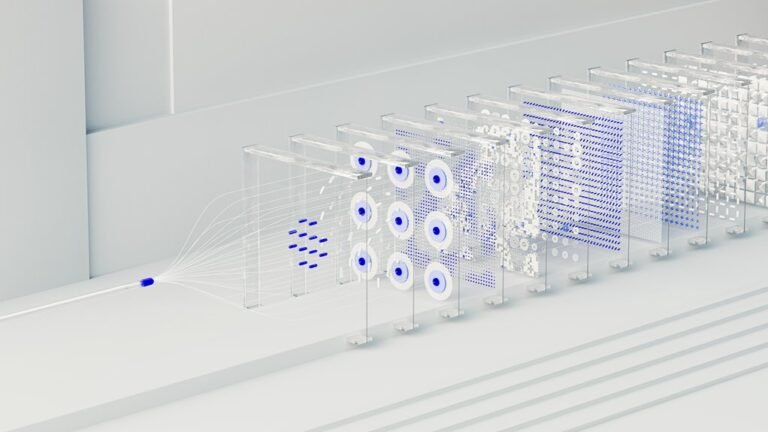
How Activity Logs Are Collected and Structured
How are activity logs gathered and organized within monitoring systems to ensure traceability and integrity? Systemically, data packets, call metadata, and event timestamps are captured at source, then standardized through log normalization to ensure consistency.
Logs are stored immutably, tagged with provenance, and subjected to access controls to protect data privacy while enabling auditability and accurate reconstruction of incidents.
Best Practices for Documentation and Compliance
Best practices for documentation and compliance center on establishing clear, verifiable standards for record-keeping and governance. The approach emphasizes controlled access, documentation integrity, and audit readiness, ensuring consistent processes across departments. Emphasis on privacy controls and data retention supports lawful handling and accountability. Documentation should reflect formal policies, regular reviews, and traceable approvals to sustain compliance and operational trust.
Tools, Metrics, and Audit-Ready Reporting
Call monitoring and activity logs are integrated into a formal framework, enabling independent verification, traceability, and accountability while preserving freedom to audit and improve processes.
Conclusion
This article underscores that 8007025d signifies a critical disruption in call monitoring, demanding meticulous reconstruction of events and rigorous verification of oversight integrity. Activity logs must be collected, standardized, and immutably stored with provenance and access controls to guarantee reproducibility and compliance. By adhering to disciplined documentation practices, organizations ensure audit-ready reporting and defensible incident timelines. The approach is precise, and the implications are monumental—like a lighthouse in a storm, guiding governance through the darkest data.