User Account Overview Linked to Sambemil Vezkegah and Alerts Logs
The Sambemil Vezkegah account structure presents layered roles, clear ownership, and an auditable trail. Alerts and logs capture time-stamped access events, devices, and durations, enabling pattern recognition and anomaly detection. This framework supports compliance, incident response, and governance through reproducible evidence. Ambiguities in privileges or gaps in logging can undermine oversight, signaling the need for tight controls and continuous tuning. The next considerations will address how to sharpen monitoring and resolve discrepancies.
What the Sambemil Vezkegah Account Structure Reveals
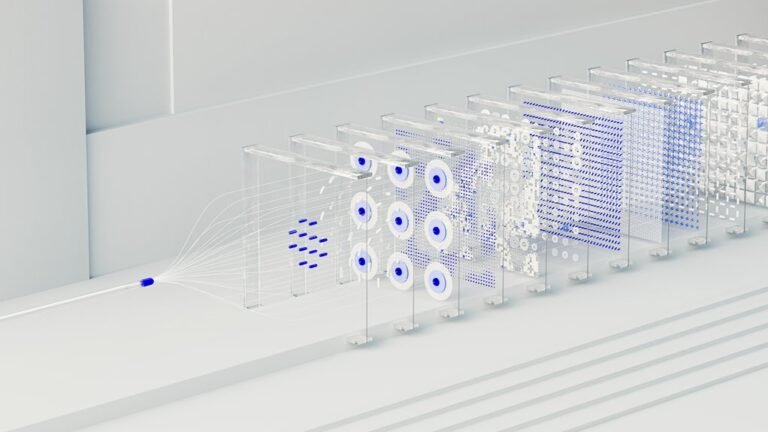
The Sambemil Vezkegah account structure reveals a layered approach to access and authorization, with distinct roles mapped to specific permissions and audit trails. It supports disciplined governance, clarifying responsibilities and limiting privilege escalation.
Discrepancy diagnosis emerges through defined access patterns, enabling rapid detection of anomalies.
Consistent role assignment preserves accountability, while scalable controls adapt to evolving organizational needs without compromising security.
How Alerts Logs Track Access Patterns and Anomalies
Alerts logs provide a structured view of who accessed the Sambemil Vezkegah account, when, and under what context. They record access events, durations, and device tangibles, enabling the analysis of access patterns. This enables anomalies detection, pinpointing unusual times or sources. The data informs incident response, guiding containment, verification, and recovery with disciplined, methodical scrutiny. Freedom through transparent telemetry.
Interpreting Key Events for Compliance and Incident Response
Interpreting key events for compliance and incident response requires translating access logs into actionable insights. The analysis emphasizes reproducible steps, evidence trails, and auditable timelines, aligning with governance needs. It examines events within the account structure, correlates alerts logs with user actions, and flags deviations. Clear documentation supports rapid containment, accurate reporting, and proactive risk reduction for freedom-minded organizations.
Best Practices for Monitoring, Tuning, and Resolving Discrepancies
Monitoring, tuning, and discrepancy resolution require a structured, evidence-driven approach to maintain reliable user account visibility.
The section presents focused guidance on actionable steps, ensures reproducibility, and reduces ambiguity.
It outlines discussion ideas and core monitoring best practices, emphasizes baseline establishment, anomaly detection, and timely remediation, and promotes transparent communication while preserving empowerment and professional autonomy across teams.
Conclusion
The account framework forms a quiet, architectural lattice—every badge of access a measured brick, each alert a careful chisel mark. Logs glow like night-watch lanterns, tracing footsteps across a mapped floor of devices and timestamps. Patterns emerge with clinical clarity, anomalies spotted as subtle fissures in the facade. In this disciplined mosaic, compliance anchors the structure, while incident response traces its shadows, moving from detection to resolution with methodical certainty. A reproducible timeline, standing firm against disruption.